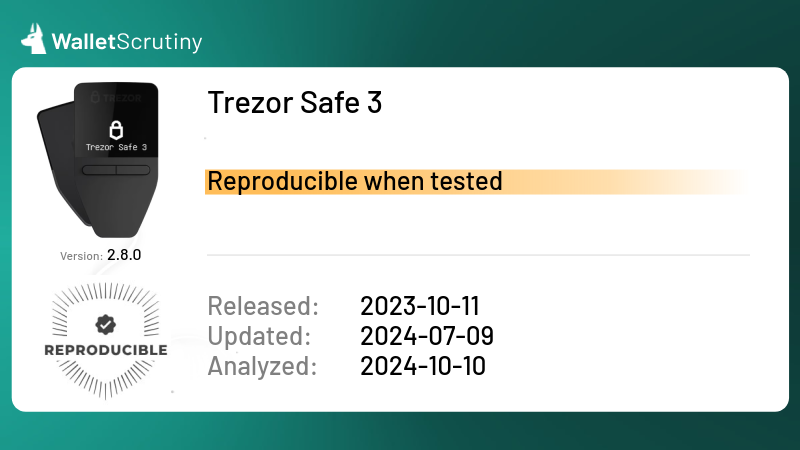
Trezor Safe 3
Our wallet review process
We examine wallets starting at the code level and continue all the way up to the finished app that lives on your device. Provided below is an outline of each of these steps along with security tips for you and general test results.
Released
12th October 2023
Custody
Private keys generated and held by user
As part of our Methodology, we ask: Is the provider ignorant of the keys?
The answer is "yes". Private keys are generated by the user on the wallet.
Read more
Application build
If you have a binary for a version that doesn't appear on the list, you can dropselect the file here to register it so somebody can verify its reproducibility:
Passed all 10 tests
We answered the following questions in this order:
The answer is "yes".
If the answer were "no", we would mark it as "Fake" and the following would apply:
The answer is "no". We marked it as "Fake".
We did not ask this question because we failed at a previous question.
If the answer were "no", we would mark it as "Fake" and the following would apply:
The bigger wallets often get imitated by scammers that abuse the reputation of the product by imitating its name, logo or both.
Imitating a competitor is a huge red flag and we urge you to not put any money into this product!
The answer is "yes".
If the answer were "no", we would mark it as "Announced but never delivered" and the following would apply:
The answer is "no". We marked it as "Announced but never delivered".
We did not ask this question because we failed at a previous question.
If the answer were "no", we would mark it as "Announced but never delivered" and the following would apply:
Some products are promoted with great fund raising, marketing and ICOs, to disappear from one day to the other a week later or they are one-man side projects that get refined for months or even years to still never materialize in an actual product. Regardless, those are projects we consider “vaporware”.
The answer is "yes".
If the answer were "no", we would mark it as "Un-Released" and the following would apply:
The answer is "no". We marked it as "Un-Released".
We did not ask this question because we failed at a previous question.
If the answer were "no", we would mark it as "Un-Released" and the following would apply:
We focus on products that have the biggest impact if things go wrong and while pre-sales sometimes reach many thousands to buy into promises that never materialize, the damage is limited and there would be little definite to be said about an unreleased product anyway.
If you find a product in this category that was released meanwhile, please contact us to do a proper review!
The answer is "yes".
If the answer were "no", we would mark it as "Not a wallet" and the following would apply:
The answer is "no". We marked it as "Not a wallet".
We did not ask this question because we failed at a previous question.
If the answer were "no", we would mark it as "Not a wallet" and the following would apply:
If it’s called “wallet” but is actually only a portfolio tracker, we don’t look any deeper, assuming it is not meant to control funds. What has no funds, can’t lose your coins. It might still leak your financial history!
If you can buy Bitcoins with this app but only into another wallet, it’s not a wallet itself.
The answer is "yes".
If the answer were "no", we would mark it as "A wallet but not for Bitcoin" and the following would apply:
The answer is "no". We marked it as "A wallet but not for Bitcoin".
We did not ask this question because we failed at a previous question.
If the answer were "no", we would mark it as "A wallet but not for Bitcoin" and the following would apply:
At this point we only look into wallets that at least also support BTC.
The answer is "yes".
If the answer were "no", we would mark it as "Provided private keys" and the following would apply:
The answer is "no". We marked it as "Provided private keys".
We did not ask this question because we failed at a previous question.
If the answer were "no", we would mark it as "Provided private keys" and the following would apply:
The best hardware wallet cannot guarantee that the provider deleted the keys if the private keys were put onto the device by them in the first place.
There is no way of knowing if the provider took a copy in the process. If they did, all funds controlled by those devices are potentially also under the control of the provider and could be moved out of the client’s control at any time at the provider’s discretion.
The product cannot be independently verified. If the provider puts your funds at risk on purpose or by accident, you will probably not know about the issue before people start losing money. If the provider is more criminally inclined he might have collected all the backups of all the wallets, ready to be emptied at the press of a button. The product might have a formidable track record but out of distress or change in management turns out to be evil from some point on, with nobody outside ever knowing before it is too late.
The answer is "yes".
If the answer were "no", we would mark it as "Leaks Keys" and the following would apply:
The answer is "no". We marked it as "Leaks Keys".
We did not ask this question because we failed at a previous question.
If the answer were "no", we would mark it as "Leaks Keys" and the following would apply:
Some people claim their paper wallet is a hardware wallet. Others use RFID chips with the private keys on them. A very crucial drawback of those systems is that in order to send a transaction, the private key has to be brought onto a different system that doesn’t necessarily share all the desired aspects of a hardware wallet.
Paper wallets need to be printed, exposing the keys to the PC and the printer even before sending funds to it.
Simple RFID based devices can’t sign transactions - they share the keys with whoever asked to use them for whatever they please.
There are even products that are perfectly capable of working in an air-gapped fashion but they still expose the keys to connected devices.
This verdict is reserved for key leakage under normal operation and does not apply to devices where a hack is known to be possible with special hardware.
The product cannot be independently verified. If the provider puts your funds at risk on purpose or by accident, you will probably not know about the issue before people start losing money. If the provider is more criminally inclined he might have collected all the backups of all the wallets, ready to be emptied at the press of a button. The product might have a formidable track record but out of distress or change in management turns out to be evil from some point on, with nobody outside ever knowing before it is too late.
The answer is "yes".
If the answer were "no", we would mark it as "Bad Interface" and the following would apply:
The answer is "no". We marked it as "Bad Interface".
We did not ask this question because we failed at a previous question.
If the answer were "no", we would mark it as "Bad Interface" and the following would apply:
These are devices that might generate secure private key material, outside the reach of the provider but that do not have the means to let the user verify transactions on the device itself. This verdict includes screen-less smart cards or USB-dongles.
The wallet lacks either a screen or buttons or both. In consequence, crucial elements of approving transactions is being delegated to other hardware such as a general purpose PC or phone which defeats the purpose of a hardware wallet. For big exit scams, a companion app could always request two signatures - one for the coffee you are paying and a second to empty your wallet completely. The former could be broadcast while the latter only gets collected for later use.
Another consquence of a missing screen is that the user is faced with the dilemma of either not making a backup or having to pass the backup through an insecure device for display or storage.
The software of the device might be perfect but this device cannot be recommended due to this fundamental flaw.
The product cannot be independently verified. If the provider puts your funds at risk on purpose or by accident, you will probably not know about the issue before people start losing money. If the provider is more criminally inclined he might have collected all the backups of all the wallets, ready to be emptied at the press of a button. The product might have a formidable track record but out of distress or change in management turns out to be evil from some point on, with nobody outside ever knowing before it is too late.
The answer is "yes".
If the answer were "no", we would mark it as "No source for current release found" and the following would apply:
The answer is "no". We marked it as "No source for current release found".
We did not ask this question because we failed at a previous question.
If the answer were "no", we would mark it as "No source for current release found" and the following would apply:
A wallet that claims to not give the provider the means to steal the users’ funds might actually be lying. In the spirit of “Don’t trust - verify!” you don’t want to take the provider at his word, but trust that people hunting for fame and bug bounties could actually find flaws and back-doors in the wallet so the provider doesn’t dare to put these in.
Back-doors and flaws are frequently found in closed source products but some remain hidden for years. And even in open source security software there might be catastrophic flaws undiscovered for years.
An evil wallet provider would certainly prefer not to publish the code, as hiding it makes audits orders of magnitude harder.
For your security, you thus want the code to be available for review.
If the wallet provider doesn’t share up to date code, our analysis stops there as the wallet could steal your funds at any time, and there is no protection except the provider’s word.
“Up to date” strictly means that any instance of the product being updated without the source code being updated counts as closed source. This puts the burden on the provider to always first release the source code before releasing the product’s update. This paragraph is a clarification to our rules following a little poll.
We are not concerned about the license as long as it allows us to perform our analysis. For a security audit, it is not necessary that the provider allows others to use their code for a competing wallet. You should still prefer actual open source licenses as a competing wallet won’t use the code without giving it careful scrutiny.
The product cannot be independently verified. If the provider puts your funds at risk on purpose or by accident, you will probably not know about the issue before people start losing money. If the provider is more criminally inclined he might have collected all the backups of all the wallets, ready to be emptied at the press of a button. The product might have a formidable track record but out of distress or change in management turns out to be evil from some point on, with nobody outside ever knowing before it is too late.Application information
Advanced hardware security and fully open-source code protect millions of Trezor users every day.
Source: Website
Device Description
The Trezor Safe 3 is a secure hardware wallet that combines a certified EAL6+ Secure Element chip with an open-source design for enhanced protection of digital assets. It features a 0.96” monochrome OLED display, USB-C connectivity, and two-button input for on-device transaction confirmation and passphrase/PIN entry. The wallet supports 12-, 20-, and 24-word backup options, including advanced Multi-share Backup, and integrates with the Trezor Suite app for managing, trading, staking, and tracking thousands of supported cryptocurrencies. Privacy features include Tor support and coin control, while authentication standards include FIDO2 and 2FA. Built with durable materials and tamper-evident casing, the Safe 3 offers a robust cold storage solution in a compact and modern design.
Previous Review 2024-04-01
This is the latest model of the Trezor hardware wallets and it does feature a
so called “secure element” or SE in short. With that, our first worry is if we
have a firmware to review at all. Popular products like the
![]() Ledger Nano S
trade
transparency for “security” by running their sofware on chips where the provider
does not allow them to disclose the source, putting the provider in a position
where any update could put funds at risk with no way of independent scrutiny.
Ledger Nano S
trade
transparency for “security” by running their sofware on chips where the provider
does not allow them to disclose the source, putting the provider in a position
where any update could put funds at risk with no way of independent scrutiny.
As Trezor has been struggling with these SEs for a long time, to the point of working on their own SE that would allow scrutiny, while always working with truely open source, this product is probably doing the right thing, too. But … how can we verify?
It took quite long to find mentions of firmware verifiability for the Trezor Safe 3 but as metioned in a reply to this issue,
the Safe 3 firmware is the same type and format as the TT so the exact same instructions apply.
the only change (which we do need to document) is that the path to the TS3 binary is
build/core-r/fimware/firmware.bin, and similarly for the model T the path changes tocore-t
This is great but if for example the keys get created by only the SE, we are back at having to trust its unknown code, right? So how exactly do they use the SE?
This article has answers.
We do not run code on the chip itself. The Secure Element simply stores a secret that can be used to decrypt the recovery seed, i.e., it never actually knows what your recovery seed is.
This is good. It implies that the SE neither generates the secret, following the
same path as for example the
![]() BitBox02
.
BitBox02
.
So, where is the firmware to be found? Quite a long search doesn’t yield a binary to download and their chatbot appears to not understand us neither.
In the repo where we can
find the firmware for their other products, we can see cryptic descriptors
t1b1, t2b1 and t2t1 which according to
this code
translate as follows:
TREZOR_ONE = T1B1
TREZOR_T = T2T1
TREZOR_R = T2B1
TREZOR_SAFE3 = T2B1
TREZOR_T3T1 = T2B1
TREZOR_DISC1 = DISC1
TREZOR_DISC2 = DISC2
An issue has been opened at https://github.com/trezor/trezor-firmware/issues/4586
Product page updated by Daniel Andrei R. Garcia, Leo Wandersleb, keraliss
Do your own research
In addition to reading our analysis, it is important to do your own checks. Before transferring any bitcoin to your wallet, look up reviews for the wallet you want to use. They should be easy to find. If they aren't, that itself is a reason to be extra careful.